Cyber Maturity Assessment
Take your cyber security capability to the next level with a bespoke Cyber Maturity Assessment.
At Byte™ we have the knowledge and practical experience to provide you with a definitive assessment of your cyber maturity. But, not only that, we will define package of work to drive tangible and measurable improvements. Helping you undertake the work required to have the most effective return in maturity growth for your organisation. This is not a one size fits all approach, but taking common components and applying the uniqueness of your organisation with our experience to delivery a meaningful outcome.
Navigating the world of cyber can be a daunting undertaking. We at Byte™ are hoping to simplify that process, by bringing our experience alongside a concise operating model from which to assess and then plot your journey.
Securing budgets and knowing what expenditure will bring the greatest risk rewards can be an absolute minefield. With our methodology you can quickly visualise which pieces of your capability jigsaw are missing and establish incisive actions, in the right order, to drive material growth in critical areas.
With Byte™ you are just three steps from realising your journey.
One model. Many views.
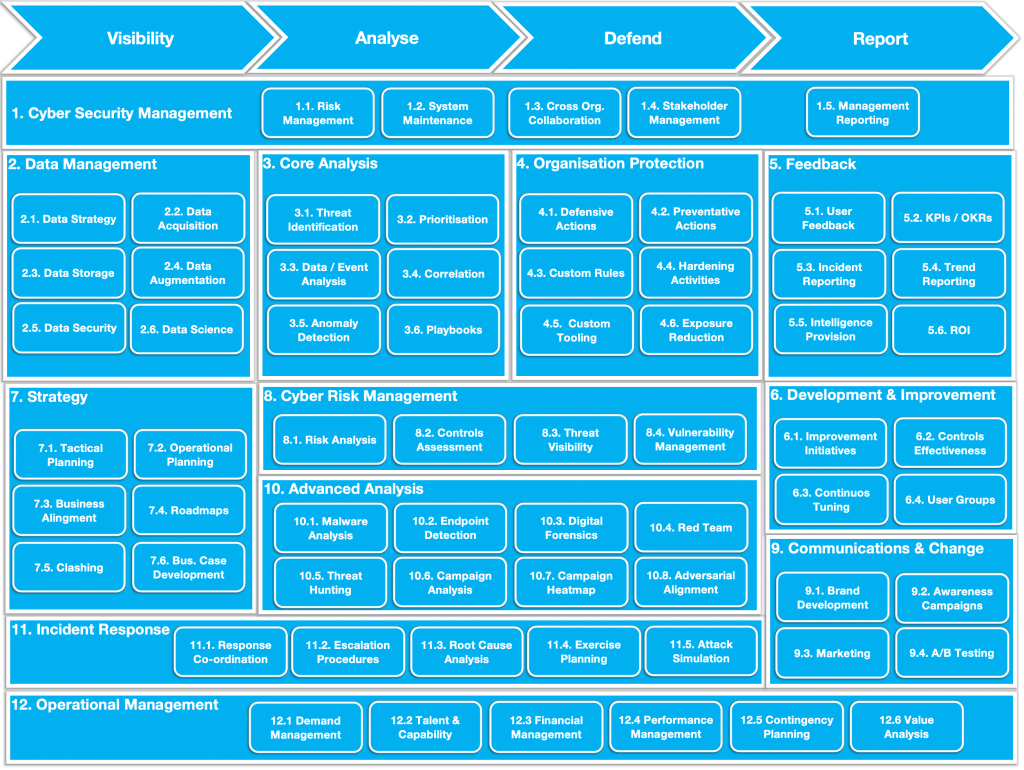
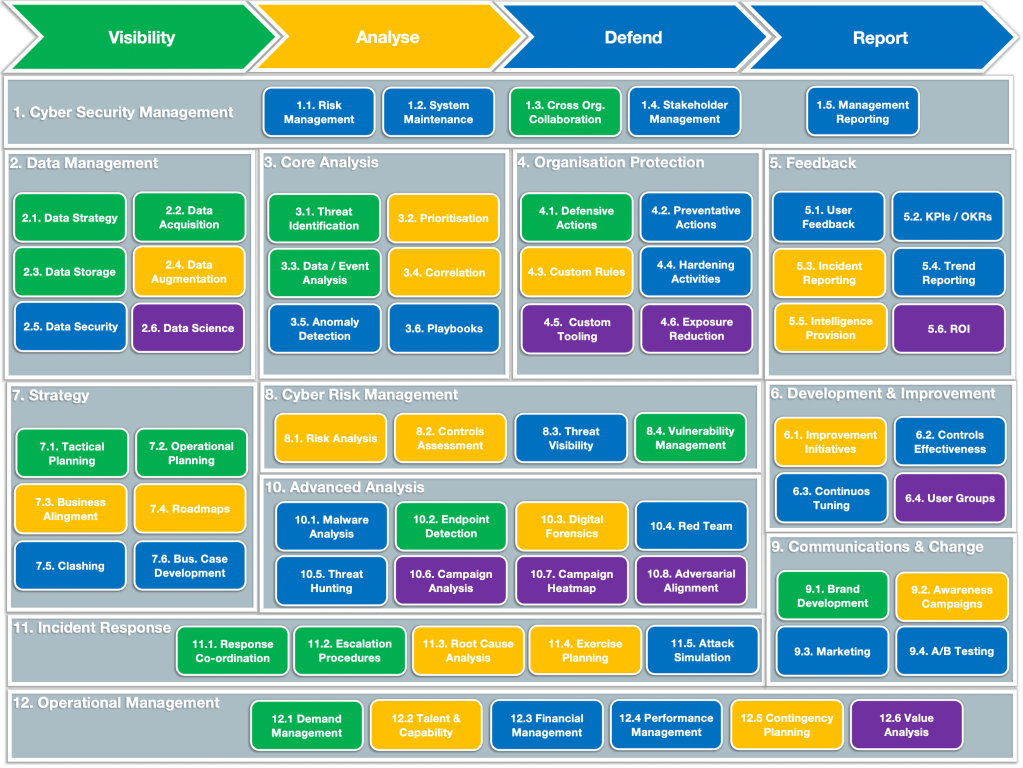
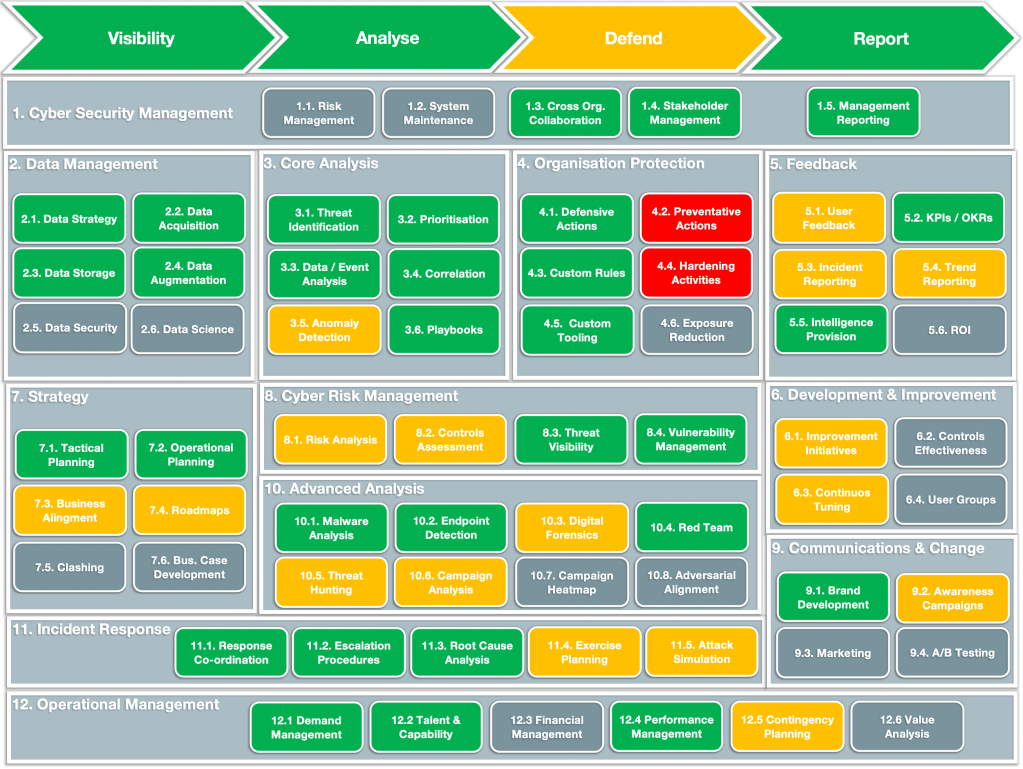
1. Target Operating Model
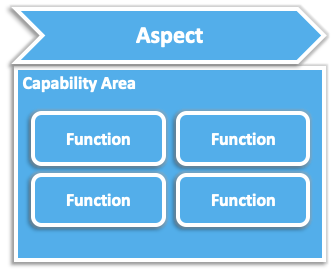
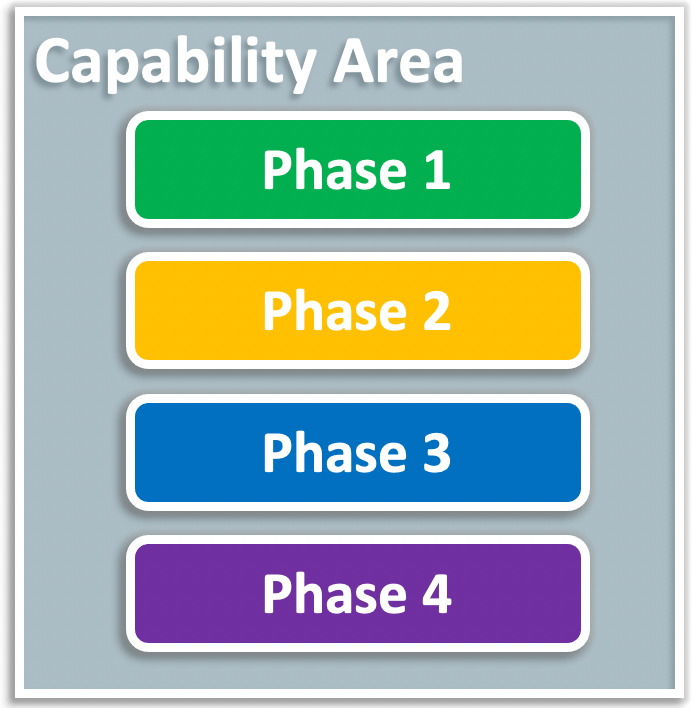
We have developed a model that caters for the full gamut of cyber capabilities. The model provides a top level capability, underlying functions, that each in turn are made up of several supporting components. The model has been designed from mixing best practice / standards with the knowledge from practically building, maintaining and optimising cyber capabilities in multiple organisations and sectors.
Each capability within the model is designed to support an overarching aspect, which follows a natural flow from visibility to reporting. It is designed to draw out a pathway to consistent growth and greater competence. We use the same model throughout, to aid visibility at each stage, but also to simplify this rather than bamboozle with science. You can see every step of the journey with a common reference point.
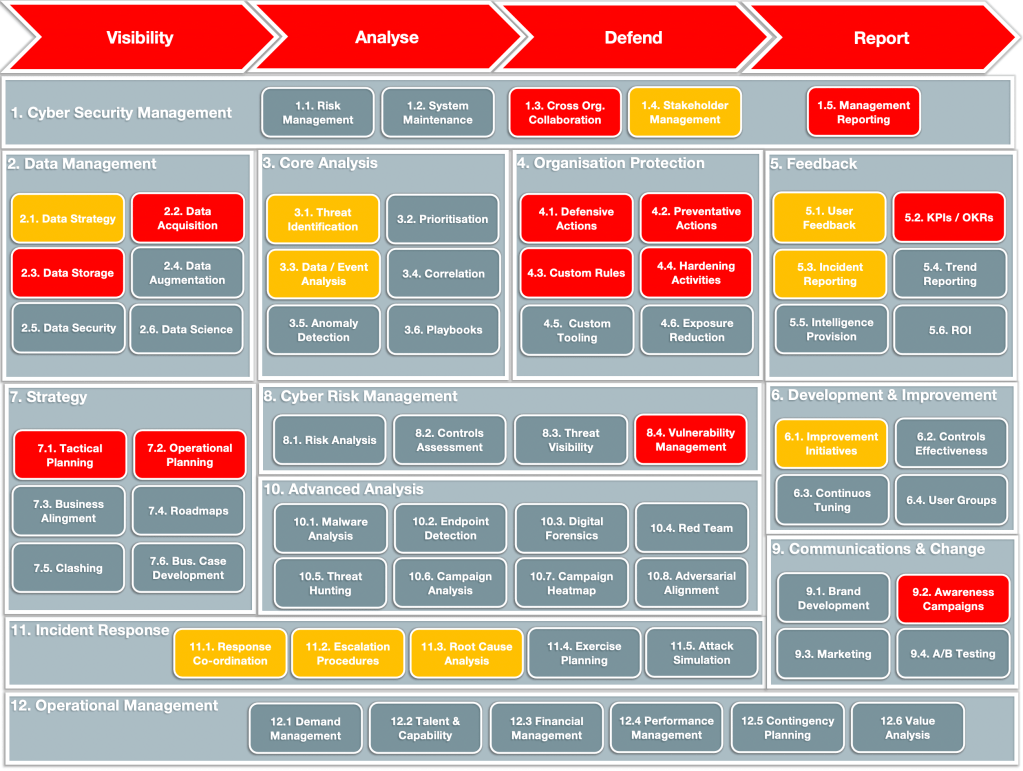
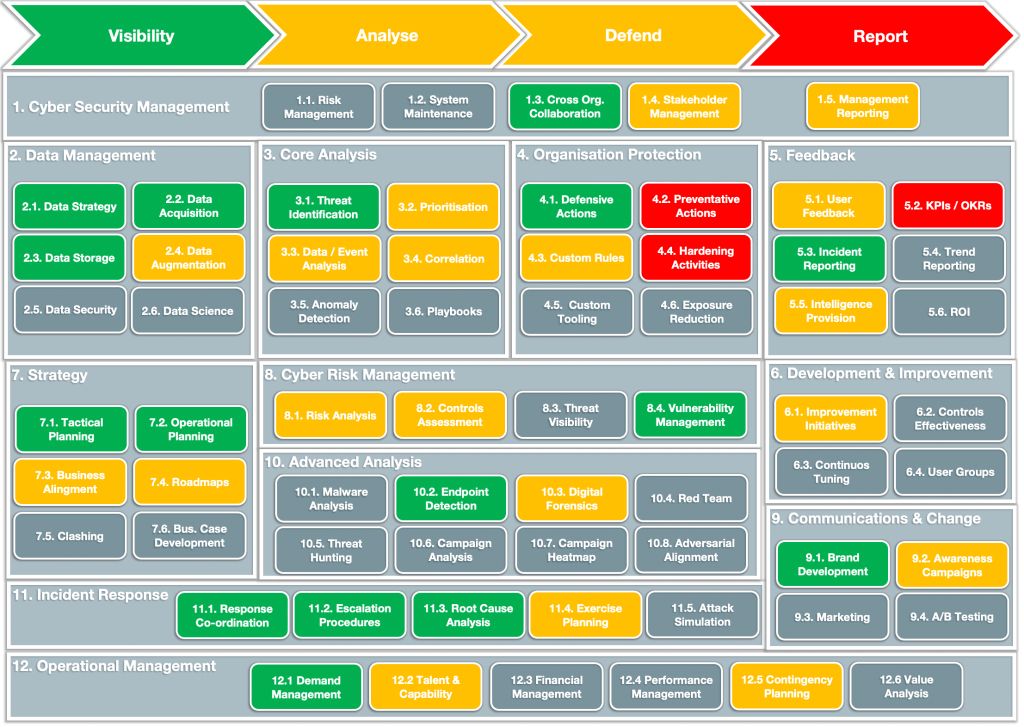
2. Capability Assessment
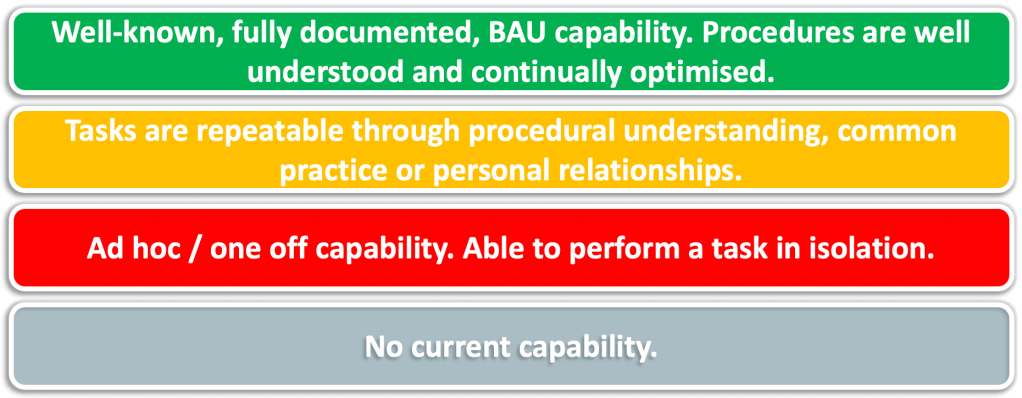
We will assess your organisations existing capabilities and provide you with a definitive view of your maturity to date. This is often a little disheartening at first, but by knowing where your genuine weaknesses lie you can do something about it. Our assessment is designed with transparency in mind. We will be full and frank, provide the evidence to back up our statements, but moreover put you in a position to drive differential change.
We will not sugar coat what we present to you. We believe in honesty and transparency. We will bring a wealth of experience to help you understand and visualise your capabilities and shortfalls.
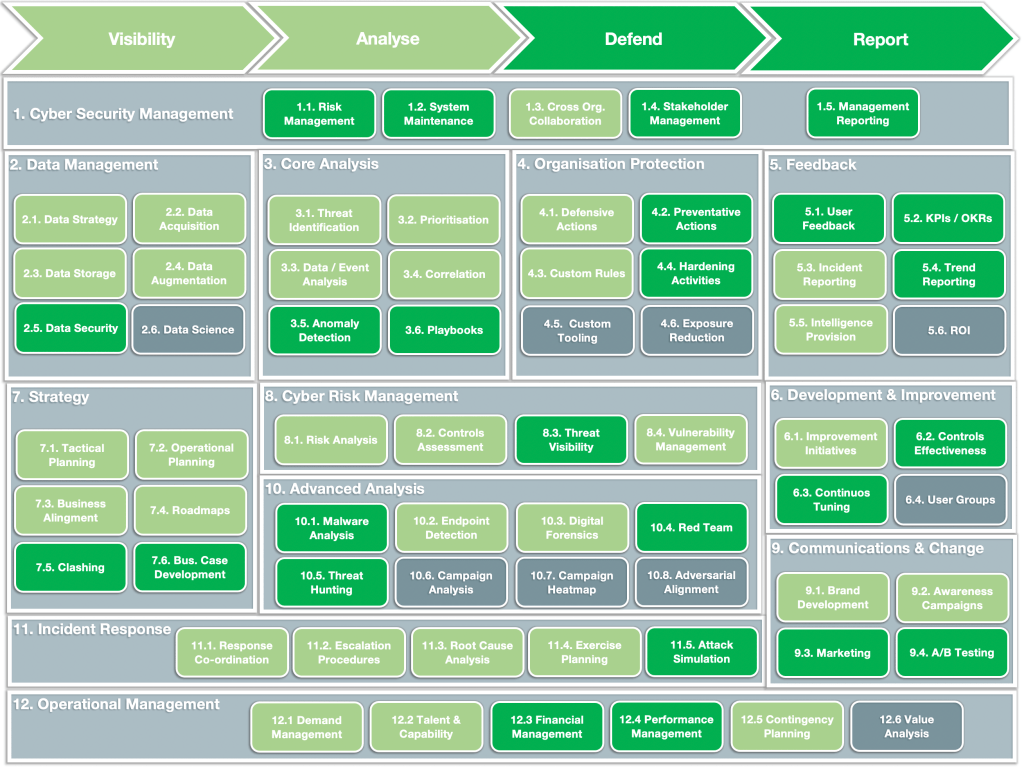
3. Improvements Planning
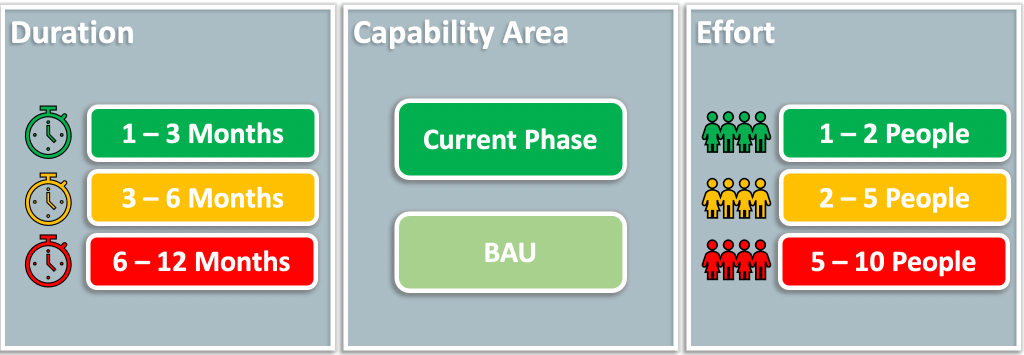
Utilising our world class expertise, we will define a bespoke plan for your organisation, to drive a maturity uplift through a series of improvement initiatives, designed to maximise and accelerate your growth trajectory. These will be defined in clear work packages, specifically detailed to match your need, and to enable you to implement the building blocks in the right order. This isn’t just about spending, or buying technology, but improving maturity and security through the appropriate mechanisms.
We understand dependencies. We understand linkage between aspects, processes, technologies and teams. We have lived and breathed this and now are presenting it to you to help you achieve the maximum return.
Taking those work packages we will help you to understand the magnitude of effort (time, material, cost and labour) as well as identifying any dependencies, so that work can be ordered for most effect. Through this approach we minimise project dwell time and ensure that delivery focus remain resolute throughout.
Working with you we will identify any potential accelerator opportunities, such as partner collaboration, technological or procedural uplifts and well as organisational constructs. We have the virtue of being solution agnostic, and thus can simply focus on you and your desired outcomes. We are here to bring that to life in operation in the smartest way possible.
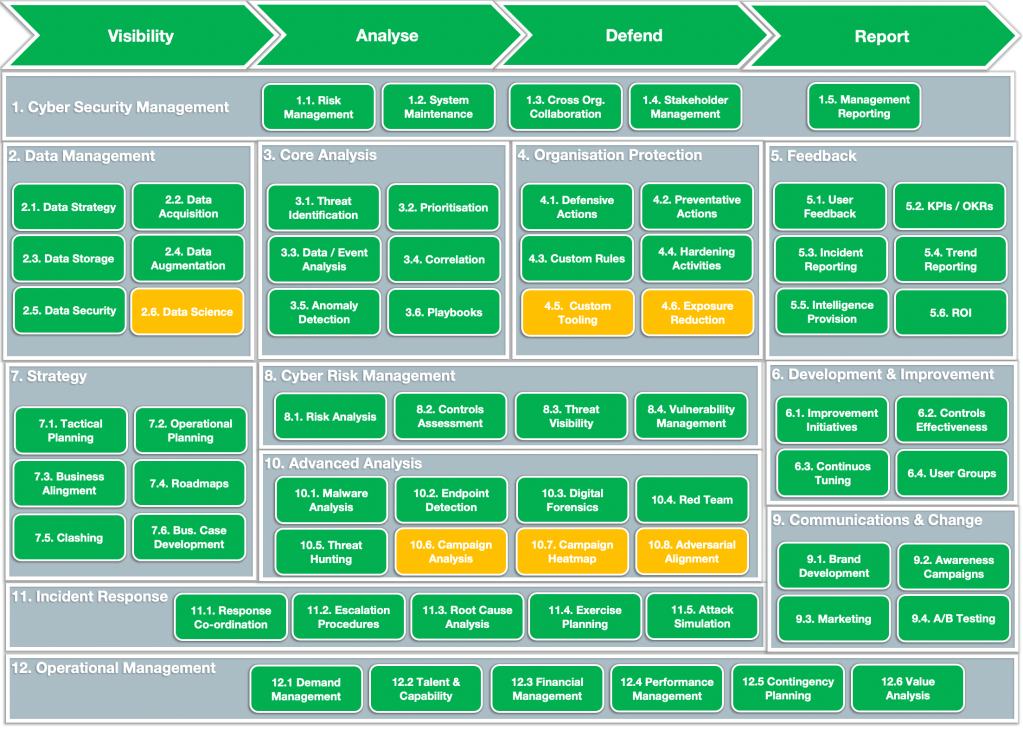
Continual Assessment
Working from the same overarching model we can help you understand how improvement initiatives will impact upon your maturity and deliver desired results. All throughout we will plot these for you, providing visualised outcomes and also identify where you start to encounter diminishing returns.
Our role is to give you the insight to make good decisions and realise the positive effects of those decisions. To do things in the right way and right order to maximise return.
Our methodology has been used to positive effect across multiple sectors, including retail, banking, Government, as well as across geographies. We are confident at Byte™ that we have the right model for you.
Seeing our existing capability laid bare before us was an eye opening experience. The fidelity that Byte™ brought out was incredible. We were able to leverage their expertise to define several distinct work packages that drove huge improvements. Moreover we could see the difference. Without Byte™ we could not have done this.
Director of Information Security Retail Organisation
What a typical Cyber Maturity Assessment engagement looks like…
It starts with understanding you as a business, your drivers and then an in-depth review of your current capabilities and existing plans. This will cover, not just people, process and technology, but also the interdependencies. We will also establish your collaboration maturity across business units in your organisation, as without this any plan is doomed to fail. Security is so much about the wider business and aspects outside of your locus of control that to not consider and embed them in any assessment is simply unacceptable.
We will provide to you and comprehensive picture of where you stand today as well as a plan for delivering telling improvements. A plan that helps you understand the building blocks and the required order to maximise growth.
All defined against the same core measurement methodology throughout, which has been built from the expertise of people who have lived and breathed cyber from the coalface.
Those improvements will be detailed in terms of effort expenditure, magnitude, timescales, as well as dependencies and limitations, as well as acceleration opportunities where applicable. This is all about providing you with the best possible return on any investments you make, and ensuring that you can be self-sufficient in determining your own outcomes, with a model that is defined specifically for you.
A typical engagement lasts between 3 and 6 months, depending on your complexity as an organisation, but all this is clearly defined from the initial engagement, so that there are no hidden traps or costs. From this you will have the power to execute at pace and with tangible results.
Our model is completely flexible. Frankly, it has to be. Because as you develop a better understanding of your risk, which you will do as you mature, then you will have better evidence backed visibility, which may well drive different business decisions. As such, any model needs to have the flexibility to mirror the risk agility you will develop. It is your model, not a one size fits all formulaic tick box exercise.
If you would like to learn more about our Cyber Maturity Assessment, then please get in touch and we can have a conversation about whether it is the right thing for you or not. https://heybyte.co.uk/contact/