For a while I have been toying with the idea of how we grow the maturity of our cyber capability across the UK. I say we as I think it is incumbent on us all to do such. And by ‘we’ I’m talking about individuals, teams, organisations, private and public sectors. A collective rethink, or mindset. Strategy and policy through operations and beyond. Like a dot to dot picture that bisects the full gamut of security as an industry. I’ve been in this industry for over two decades, across multiple sectors, including life as a vendor and founder and have largely seen incremental growth and if anything less join-up and more distancing / silos. It has to change.
Why? Simply because we have so many dependencies outside of our own organisation, that without communal growth we will continue to carry significant weaknesses beyond those within our locus of control. Couple this with the weaknesses that each organisation carries within its overall control and how difficult they are to even identify let alone address. What assets have we got by the way?
Although a somewhat of a throw away comment, this serves to highlight some major issues that we collectively face. Call it the basics or call it whatever, we all have significant weaknesses that are very hard to solve, and none will be solved overnight. Whatever we do to move forward we must always be cognisant of what we already know we’re not great at. We cannot just run off into the sunset chasing new things whilst leaving our asset inventory in a largely unknown state. It simply will not work!
Security has grown exponentially, as has technology, and yet breach after breach, many of which were utterly avoidable. A trend that is not going away, but if anything accelerating. Or certainly ther visibility, or publicity of breaches.
We all know, for example, that supply chain is a major risk factor and that in turn we also represent a cog in further supply chain risk. We have seen growth in the targeting of service providers, for that one to many threat relationship. Businesses are chaning their technological demographic. Adoption of newer concepts, or delivery methods often coupled to legacy systems. Technology growth and debt brought together. There’s a growth in the prevalence of threats and most certainly the volume of potential targets, be it human, service or device.
There are pockets of organisations, or within organisations, that are very capable in cyber security, but it is fair to say the herd is average at best. For me, that has to change.
We have an industry that is largely led by a vendor narrative, encouraging organisations to invest in distinct solutions, or a technology first spend, with little cognisance of the people and process requirements, dependencies or impacts. And a continual occurrence of threats being realised in material breaches across the globe that feeds the already well-oiled machine. We need to break the cycle of following this narrative and start building a joining between organisations, individuals, themes. Time to start thinking more for ourselves then being fed what thinking needs to happen from a position of bias like vendors or analysts. That is not to effectively block their views and insight, but also not to take it as the gospel.
For me there the biggest weakness I see is the dislocation of our efforts. By that I mean that we rarely join the dots between people, process and technology, between business departments, between user requirements, between our technology investments, between risk and operational measure, between organisations both within and without our supply chain. To join said dots requires a different lens. A wider viewpoint of problems as a whole, not just a symptom or manifestation, but the whole. And this is not just within our own organisations, but beyond into the whole community.
We know that information sharing is key. We’ve known this for a long time. Yet how many organisations actually share knowledge? How far have we got in the sharing mantra? Have we really left the runway yet?
Well back to growing communal maturity. If we can find levers to develop and drive growth across enterprises, sectors, communities in a conjoined manner then we could start to progress concepts and theories, like information sharing, common taxonomies or easily translating between taxonomies and assured patterns into more of a reality. Open up possibilities of doing this more effectively. More optimised processes and output.
At the same time focussing on developing the workforce of tomorrow and beyond, that is actually aligned with practical need. And not just defenders, but the innovators, the ideas. Developing solutions that will aid local and global problems. Buidling and accelerating the cyber export capability. By providing or creating better alignment between customers’ needs and vendors’ solutions it would help boost UK based solutions in the global market. We get that growth through joining together.
There is of course a lot of work already afoot. The outstanding contributions of the NCSC, their Active Cyber Defence programme, as just one, albeit significant example. Even then growth is predominantly driven in the public sector, when the problems are truly sector agnostic. What if we went up a level and really looked at the UK as a whole, or wider?
This is where I’ve toyed with an overall concept, as an opening vision for something like an overarching goal for cybersecurity across the UK. Something to aspire to, that with the right strategic view and enactment, could help drive a reduction in weaknesses and an uplift in protection of one and the whole.
I will caveat at this point to make it clear that this is merely a conceptual high-level model. Something to kick around, discuss and determine if it could have legs or worth developing further. There will be many reasons why this ‘won’t work’ as a knee-jerk response. But then I’d argue that what we are collectively doing today isn’t exactly working, so what’s wrong with having a more strategic view.
This is about changing the mindset.
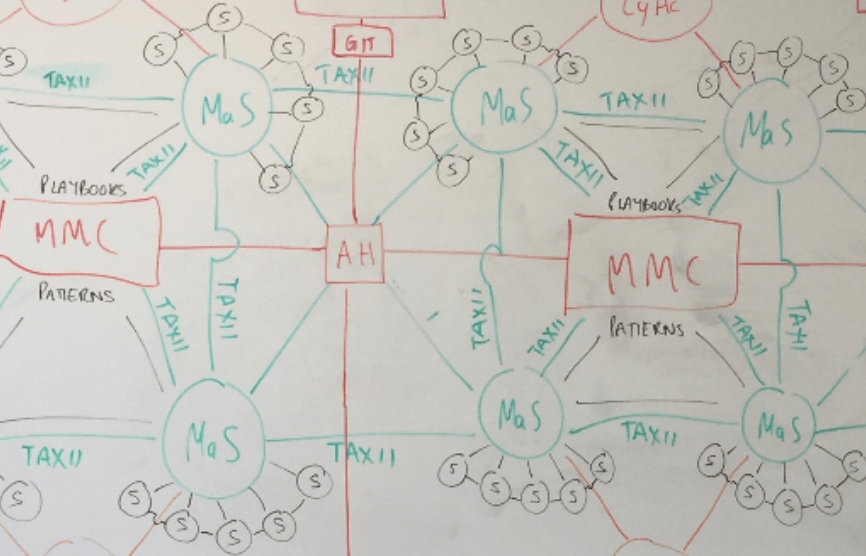
The Model
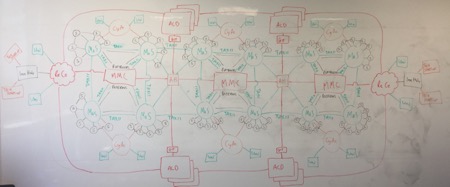
Looks busy yeah? Well it is busy! I did say it was high-level too!
What this represents is a joining together on a very large scale. Multiple components that are intrinsically linked with a common purpose of effective defence. On a quick side note I have purposely not defined any specific geography to that effective defence. Partly due to the interconnectivity of global business and operations and also so as to see how the definition could evolve alongside the idea. I’ll try and delve a little deeper into each component and the relationships between them as they stand in my head.
Please excuse the use of acronyms. Although I drew this on a VERY large whiteboard it still wasn’t big enough for the longhand names as I have called them. They are simply monikers anyway just to identify conceptually what each component is.
The main theme is that every component has linkage to every other component. Not always direct, but there is a path between them that pulls everything together and ideally in the same thematic direction. A multi-thread sown throughout the UK from the most mature the least.
This will not go into how this could be constructed as it is merely a concept to be considered. My main focus is how we can change what we do today into something far more joined up, more focussed and really more effective.
The components within the model (again apologies for acronyms!) are as follows:
Major Monitoring Centres (MMC on the diagram)
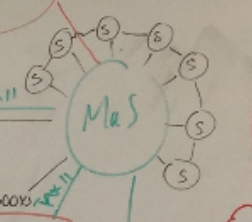
Macro Security Capability (MaS)
Micro Security Capability (S)
Acceleration Hubs (AH)
Research Centres (ReCe)
Innovation Hubs (InnHub)
Cyber Academies (CyA)
Active Cyber Defence (ACD)
Educational Facility (Uni)
Innovative UK Suppliers (Tech Startup)
There are a couple of other annotations on the diagram. TAXII is a transport service for threat intelligence. That is there to highlight a thread of sharing threat intelligence throughout the model. It is just an example of a singular thread that runs throughout.
There’s also Patterns and Playbooks. Again, these are simply illustrative aspects of knowledge sharing that should take place. Common assured methods to help drive effectiveness. Never set in stone, but readily available resources to aid growth, capability, assurance, optimisation etc.
This joinging up includes building out some of the better practices in use today. For example security champions at the heart of awareness activites in organisations. They’ve been around for over a decade, but are not actually that common to see. Or bringing awareness and operations together and helping others to understand how this can be done. Taking some of those practices and defining how as well as why and making it easily repeatable for others and then building into wider communities to create communities within communities. Or venn diagrams of communities where there is perpetual sharing and learning.
Now this is all very high-level, as I’ve already said, and that is because I want it to be a framer for discussion. This is a framer to open the dialogue and elicit views.
So, to break the components down and hopefully bring a little bit of life to a very busy picture.
Major Monitoring Centres [MMC]
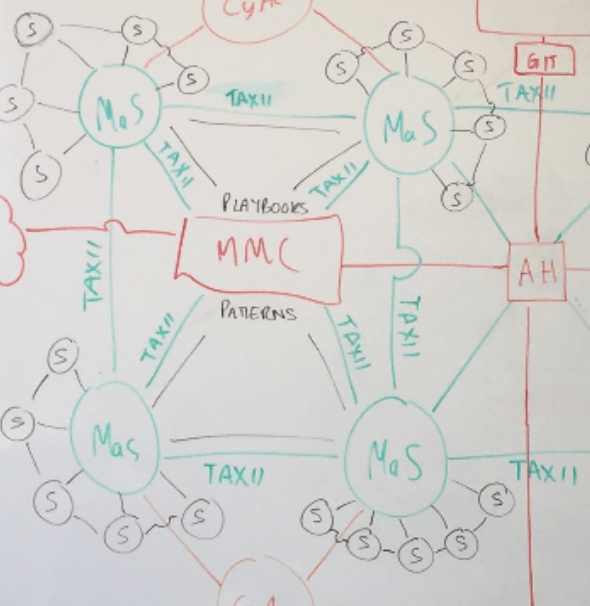
At the core I have placed three (who knows how many really) Major Monitoring Centres. Thematically they would look at aspects like:
- Central monitoring points across the UK.
- Taking data from such things as Turing (DNS) / DMARC / Threat Actors etc.
- Accelerated intel feed into Macro Security Capabilities
In essence a collection point from those with the widest visibility that can then feed meaningful and timely information into the wider community. For example, relevant threats and mitigations. Information on exploits in the wild to help prioritisation of patching. An obvious candidate in this space would be an organisation based in a round shaped building in the south-west of England; though that comes with a potential timelag, or time overhead. Government doesn’t have a history of speed, and especially those who deal at the top levels of secrecy. This is where an eye to private sector could act as the accelerator.
Now, whenever I’ve dealt with aforementioned government agency in the past, with regards to sharing, it has always felt somewhat of a one-way relationship. That’s not conducive to helping organisations defend themselves against things that matter. Which OK, is everything, but the dissemination of clear and concise information to all is a vital component in this construct. These types of organisations have the best tap points to understand more of the whole. Certainly, far more visibility that almost everyone else. This is almost a staging point for the big picture. Yes, there are considerations like scope and remit and taxonomies, but this is conceptual. Think of this as a series of umbrellas. How and in what format they inform of imminent rainfall is lower level thinking.
They would be a key feed component into a series of smaller entities.
Macro Security Capability [MaS]
Considering, for a moment, the model, I’ve placed at the centre a component called a Macro Security Capability (again ignore names as such). They would be a receiver from the MMCs and have a thematic construct of:
- Established Security Capabilitiess across private and public sector
- Able to ingest and action intel from MMC and enrich with their own knowledge
- Intel feed into Micro Security Capabilties
- Loop-back into MMC
This is the hub of this aspect of the model. Those with a more mature cyber defence approach. The ability to ingest and make sense of information feeds, further enrich it and then issue both back to centre and to sub-components. It should be noted that this is not restricted to a flow down model as any entity can interact in any direction, it is just an example flow.
As a more mature organisation you would expect them to also provide advice and guidance to aid their sub-components growth trajectory, for example playbooks. They could also potentially offer services to their subs and others where there were capability gaps. For example IR capabilities, or forensics. There is no reason why these could not contain things like managed SOCs, who already operate this model to a degree.
For the sake of diagramtic ease I have drawn this as a hub and spoke model. This is an illustrative approach used to highlight the parent / child relationship of a more mature capability nurturing effectively sub components in the model.
At this point it would be easy to fall into a particular model as being the ‘ideal’, which is not my intent. So to clarify that, although hub and spoke is used illustratively it is a completely open part to debate. Even in that does there have to be a, singular, model so long as connectivity and process was in place?
There are existing models in place, and lets face it this isn’t greenfield. It is greenfield, brownfield and frankly wilderness, which I why is do not want to prejudice this with a pre-defined view
Micro Security Capability [S]
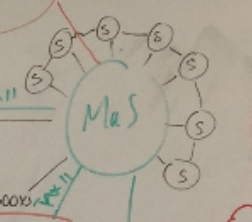
Forming the spoke of the illustration would be a series of Micro Security Capabilities. These components are of the following ilk:
- Juvenile SOC / security construct (newly established / yet to be built)
- Able to ingest intel feed from MaS and action with assistance
- Loop-back into MaS
A less mature cyber capability, receiving services of some kind from the ‘parental’ partner, be that the information feed flow to distinct services or full blown SOC services etc. No hard and fast ruleset, just a concept of more mature servicing less mature. A helpful elder sibling if you will.
Part of the concept here is to encourage effective growth of their capabilities, effectiveness and knowledge.
Acceleration Hubs [AH]
To aid that growth trajectory would be a series of Acceleration Hubs. Designed to accelerate the build and establishment of Micro Security Capabilities and delivery maturity uplifts to Macro Security Capabiltiies. A mechanism for bringing the hub and spoke together and helping to make it work with a clear vision on continual improvement in terms of relationship and organisational strength.
- Deliver understanding and common patterns for active cyber defence within an organisation
- Facilitate build and construct
- Undertakes on-boarding of organisations into the construct and active cyber defence initiatives (e.g. Turing)
There’s many way this could be constructed, with multiple pro’s and con’s, but primarily a helping hand, which could involve things like baselining, strategy, optimisation, prioritisation, board engagement ad infinitum.
Research Centres [ReCe]
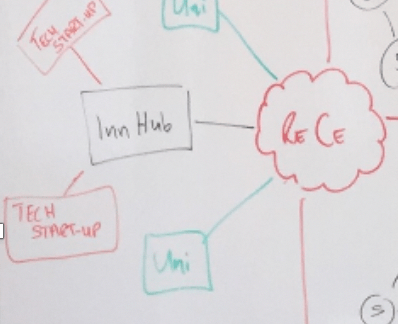
Feeding off and back into these four components would be Research Centres tasked with solving the problems of today and tomorrow. Taking elements from the big bad world of cyber and the problems faced by real organisations their focus would be on defining problems, trends, future measures etc. This is about getting ahead, if possible, of the game, but in a practical sense.
- Mix of academia, industry, suppliers and practitioners
- Designed to develop technology / process / procedures
A sub-component diagrammatically here would be the use of Educational Facilities (Uni) for part of said research. This is already an existing concept, which maybe could be taken further with greater focus on outcomes and a strategy designed to maximise capability in this space.
There is capability to open a wide variety of funding sources in this space, as well as comprehensive gains, albeit that is a damn sight easier to say than do.
Innovations Hubs [InnHub]
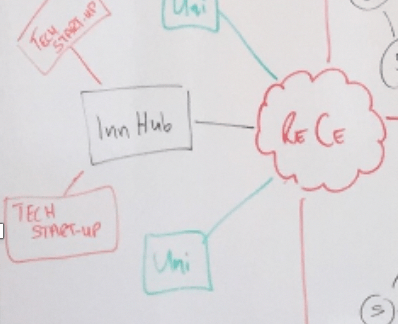
Closely linked to the Research Centres would be Innovation Hubs driven by designing the technological jigsaw pieces for real world problems and the innovation of tomorrow.
- Mix of academia, industry and tech start-ups
- Incubation
- Blue sky approach
Feeding into and creating within the startup scene with obvious collaboration with, or from the accelerator programmes that exist today, such as Wayra, LORCA or CyLon etc. Ideally here we would see solutions created that have clear usability from the outset. Solutions fitting actual problems rather than theoretical solutions looking for a problem that might in some way fit. This in turn helps the UK develop an ecosystem of Innovative UK Suppliers (Tech Startup), a platform for establishment and growth, and a whole series of potential customers with a clear problem requirement match. And of course, those problems would largely go way beyond the UK, so hopefully giving them a solid footing for wider expansion and growth of the UK cyber ecosystem on the global marketplace.
Cyber Academy [CyA]
Of course, in the midst of this there will be a requirement for people in all facets coupled with an already (allegedly) enormous skills gap. To help address some of this there would be a number of Cyber Academies. Notionally this could be geographically focussed to service those in need of talent in a particular region with local talent, however people m igrate all the time, for education, work and other reasons. Although there could be geographical or regional ties a virtual construct makes far more sense with a migratory and technology focus. We have seen very recently that remote, or virtual, is not a constriction and nor should it be in our thinking.
- Virtual construct
- Linked into University programmes [Uni] and wider educational facilities
- Provides theoretical learning
- Facilitates rotation of academy students into MMCs / Macro Security Capabilities to consolidate theory, accelerate skills build through practical hands on experience
- Develops a talent lake of suitable candidates upon graduation
An aspect that is often overlooked in this space is the need to develop practical and theoretical learning together. The feed into Macro and Micro Security Capabilities would provide the hands-on exposure to couple with theory. This could equally be provision into Research Centres, Innovation Hubs, or any component. This construct is as much about retrain as it is young talent. This is about providing environments, training and experience to a budding workforce be they school leavers, unemployed, forces personnel, career changers and all.
Utilising this resource approach brings together hands on experience gain, adding value to organisations and the people, but without adding risk. A mechanism to help feed the machine. And not just technical!!! Cyber is far more than just a technical discipline!
These components are also a mechanism for training existing employees, providing exercise capabilities for both offensive and defensive teams, management and wider.
Active Cyber Defence [ACD]
If the Major Monitoring Centres are the umbrella, then Active Cyber Defence is the programmatic connector that glues everything together. Providing and promoting overarching strategies to improve everyone. Build upon things like the promotion of DMARC, but for all, whilst providing the help, guidance and tools to make this happen.
- Defining the programmes of work to underpin the construct.
- Developing patterns, playbooks, technology, standards, guidance for all.
Taking feeds from the real world, other nations, research output and helping to frame that into cohesive bodies of work that aids the protection of all, or sectors, or specific organisations where it fits.
This is the ongoing programme of work for UK organisations to roadmap into their individual strategies.
SO….
That is what is in my head and what my experience tells me. All of this is designed to open a conversation. A gathering of ideas. To bring people together. There are definite gains to be made across the gamut of cyber security and that should include collegiate action, as individuals and organisations.
There’s other aspects to discuss like Communities of Interest or ISACs (Information Sharing and Analysis Centres) and how these might add benefit further for sector specifics and much, much more.
What I am thinking in this overall concept is that through a supporting structure everyone can win. The more mature continue maturing, gain greater visibility, become better at enriching and contextualising information which they can share with their sub’s, and of course supply chain etc., which in turn better protects their long tail. The juveniles get help to design, develop and build any cyber capability, and this help acts as an accelerator to their growth trajectory. We share common standards, patterns, knowledge, taxonomies so that we can use similar hymn sheets, talk a common language, have common understanding. Get better at risk management through continuous monitoring. Build a larger workforce with more appropriate skills matched with experience. Invigorate the already burgeoning cybersecurity startup scene. Build clear linkage between business need, research, technology and academia. And define continual programmes of improvements measures that actually make an effective difference.